Navigating the Haze: Understanding the Impact of Marijuana on Students

Welcome to this special preview of our article, “Navigating the Haze: Understanding the Impact of Marijuana on Students.” This sneak peek offers a glimpse into the wealth of insights and […]
Navigating the Haze: Understanding the Impact of Marijuana on Students

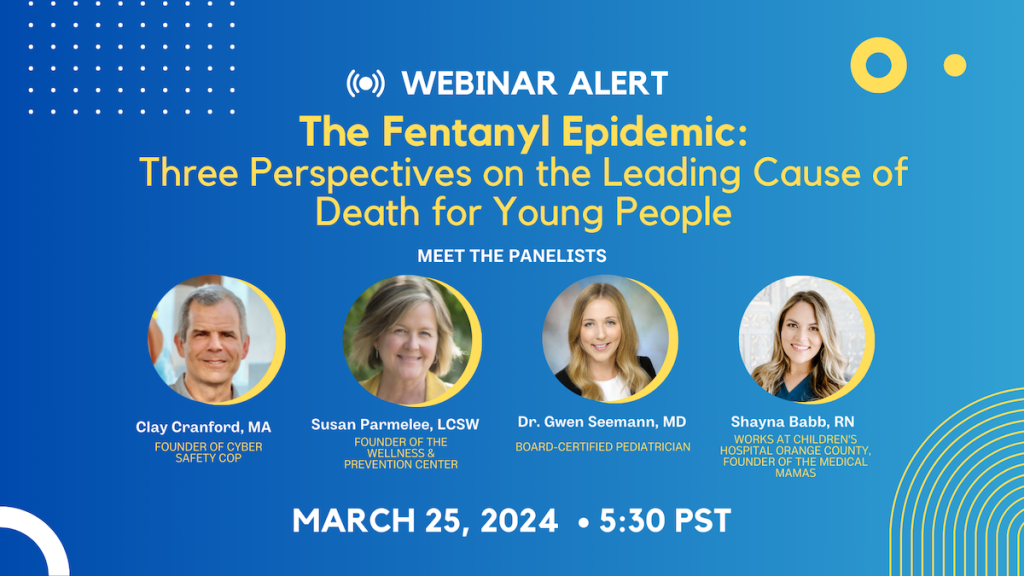
Webinar listing
Digital Dangers: Navigating Online Spaces to Prevent Sexual Exploitation
Welcome to this special preview of our article, “Digital Dangers: Navigating Online Spaces to Prevent Sexual Exploitation.” This sneak peek offers a glimpse into the wealth of insights and tips […]
Digital Dangers: Navigating Online Spaces to Prevent Sexual Exploitation
The Fentanyl Epidemic: Three Perspectives on the Leading Cause of Death for Young People